It could also be a typosquatter, where a malicious site registers domains similar to legitimate domains, in order to get traffic from people who mis-type a URL.
And, although not the case here, expired domains are often taken over by criminal sites.
About 10 years ago or so, my employer was acquired. Two years later, the new company stopped paying for the old company’s domain name. It was quickly taken over by a malware site. So old bookmarked URLs would redirect to malware-download pages.
It even affected people typing in unrelated site names, because many of us had the old domain name on our computer’s DNS domain-search list. I personally experienced this when looking for CCC pages - if I would type “bombich” into the address bar, it would get auto-completed to bombich.old_company_domain, instead of bombich.com. And once the domain-squatter took over that domain, it would send me to the malware site instead of producing a DNS error (as it did before the domain-squatter took it), which would have caused my browser to try various domain suffixes (like .com, which is what I’d want) or redirect to a web search.
It is a key part of an effective strategy, but it’s not enough.
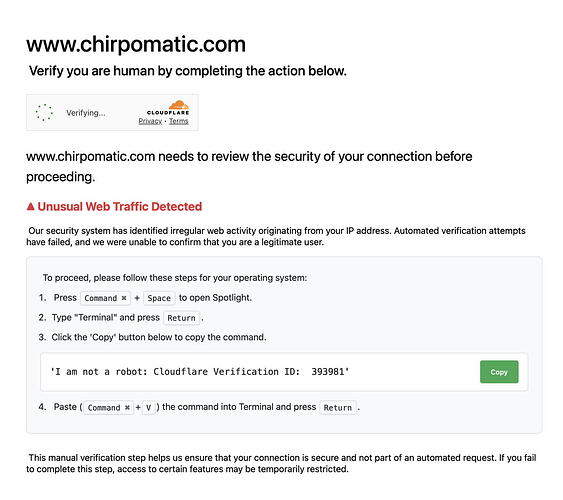
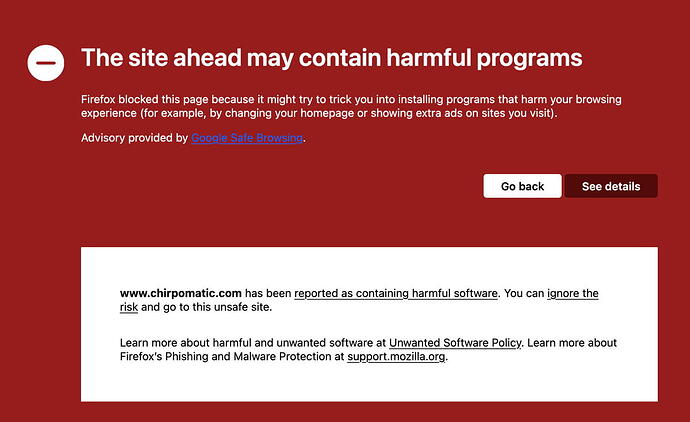
You also need to understand enough about what you’re doing and how things are supposed to work, so pages like this will set off all your red flags, so you won’t follow its instructions.
Once upon a time, the average user was much more tech savvy, because you had to be in order to get anything done. But thanks to everything being so much easier today, you can no longer assume any minimal level of expertise. So some people will require some amount of training. My employer has mandatory training courses on stuff like this, that we have to take every year. It would probably be a good idea for everybody else, but there’s no possible way to enforce such a rule for the public at large (nor would I want there to be such a rule). But perhaps ISPs could send links to course material as a part of their new-subscriber package.
Keeping all your software up to date is also critically important for protecting against malware that might not require your participation.
And, although not strictly necessary, running software to filter/block malware (ad blockers, or anti-malware software) can also help quite a bit.