Originally published at: Apple’s Certificate-Extension Updates Continue for Older Operating Systems - TidBITS
Apple has released another batch of updates for older versions of its operating systems (see “Apple Releases OS 26.2.1 for AirTag 2, Extends Certificates on Older Versions,” 26 January 2026). Release notes for most of them largely match those from previous releases, differing only in the use of the term “certification” instead of “certificate.”
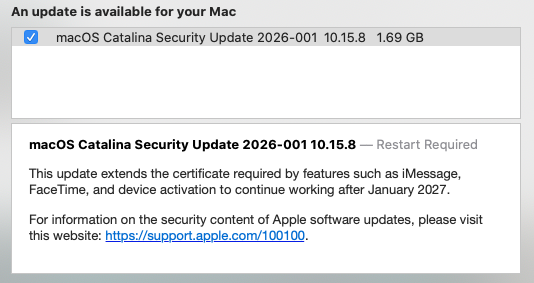
This update extends the certification required by features such as iMessage, FaceTime, and device activation to continue working after January 2027.
The full set of releases includes:
- iOS 16.7.14 and iPadOS 16.7.14
- macOS Big Sur 11.7.11
- macOS Catalina 10.15.8
- watchOS 10.6.2
- watchOS 9.6.4
- watchOS 6.3.1
The Sixteen Stumper
When Apple finally issued release notes for iOS 16.7.14 and iPadOS 16.7.14 several days later, they matched the notes for iOS 16.7.13 and iPadOS 16.7.13, which said:
This update provides important bug fixes and is recommended for all users.
TidBITS reader David Duke wrote in after our previous article to note that iOS 16.7.13 included additional release notes in Australia, so it did indeed contain important bug fixes, probably in addition to the extended certificate:
This update addresses a mobile network issue for iPhone X and iPhone 8 models when establishing a connection to emergency services in Australia.
Australian cellular carrier Telstra has a support note about this situation:
We’re currently investigating an issue preventing some older Apple devices from connecting to our network. We’re working on this as a priority with Apple and will share updates as we have them.
Devices that may be impacted:
- iPhone 8 updated to iOS 16.7.13
- iPhone 8 Plus updated to iOS 16.7.13
- iPhone X updated to iOS 16.7.13
Telstra says on that page that other iOS versions are also impacted, suggesting that we may see additional releases once Apple figures out the glitch with the Telstra network:
Apple has paused software updates released this week for some older iPhone models while they investigate. These include iOS 18.7.4, iOS 16.7.13, iOS 15.8.6, iOS 12.5.8
David Duke wrote again to report that iOS 16.7.14 restored his iPhone 8’s functionality on the Telstra network (he implied it was more than just emergency services), so it appears that Apple has finally fixed that problem. We’ll see if it triggers additional updates for Australian users of older iPhones.
The Catalina Conundrum
Interestingly, macOS 10.15.8 Catalina was not included in the list of new releases on the Apple Security Updates page—they all lack CVE entries—but that page does include Security Update 2026-001 Catalina. I can’t find any additional information about that security update, but TidBITS reader Jose Hill posted a screenshot showing the security update and the certificate extension language. So maybe Apple is delivering macOS Catalina 10.15.8 through a security update?