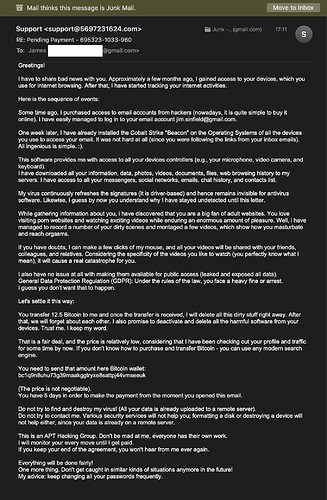
I got one of these in late October also, mine didn’t give the password they supposedly had. Some things about the mail that signaled “fake” to me were how it carefully avoided including any specific information at all that might have shown they knew “anything” about me. It says we hacked your “operating system”, not mentioning if it is Windows, Mac, or other. It says we accessed your “social accounts”, not mentioning any specific social accounts like Facebook etc. It says we hacked your email, browsing history, contacts, photos and videos, files from your computer, porn sites, etc, etc, yet of all that stuff they supposedly hacked, the email includes no reference to any actual information that from any of my contacts, photos, history, files. It seems to me if they had all that information, I would have expected at least one bit of all that information to have made it into their message to me, even if inadvertently. It would seem to me the fact that there isn’t one bit of actual information about me in the email, is most likely not due to then just not mentioning it, but the most likely explanation is that in fact they have no actual information about me. I would expect since a blackmailer wants to get someone to pay them blackmail, they would make at least a minimal effort to demonstrate that they actually had some blackmail information on you, and if they don’t do that, it’s most likely because they have no such information.
Hi all (long time)
Just a quick data point. I’ve gotten a half dozen of these over the last month or so. They were sent to (and from) an address of one of my own domains.
Rather than blocking the address, I revisited my DMARC records and upped the policy from “none” to “quarantine” (DMARC are instructions mail services may follow if someone spoofs the from address, among other failures; Adam wrote about it here in 2014). Even if set to “reject” my provider does not actually reject mail, it just ups the spam handling signals.
What I found interesting is that I received another one today, virtually identical, but not from my address this time. (Some of previous examples bragged that they were using my account to send the mail as “proof” my account was compromised.)
Anyway, I’m left wondering if the attack might be sophisticated enough to actually check the DMARC policy and adjust to avoid possible rejection or quarantine. I’ll keep monitoring for now and eventually block the address.
I seriously doubt that any of them actually came from your domain. What appears as the "From: " address is almost always faked, ignored and isn’t relevant. You have to look at the header information to determine exactly where it originated and the intermediate locations it passed through. I use https://www.spamcop.net to assist me in this.
If you find that it actually did originate from your domain, then your e-mail has been hacked.
-Al-
The easiest way by far to do this is using spamgourmet.com (cc @mpainesyd). As others have said, I would never go back to running a mail sever, the pain is not worth it with all the options out there today. The nice thing about SpamGourmet, is that you can create email addresses on the fly, as you are filling out a registration form. No need to go to the site or a server to create a new alias or mailbox. It’s a straightforward service, well designed. I highly recommend people check it out. And, @cwilcox, it has a mechanism to allow sending from one of your addresses, too. I’ve been using it for years, and it’s really excellent.
Unfortunately, it’s not accepting new users.
Jeremy
Oh, I wasn’t aware of that. Have just had a look, and it’s upsetting news. The man who runs the site has terminal cancer and has disabled new users until he can figure out what will happen to SpamGourmet. In his position, I don’t know that I would be spending time and energy on SpamGourmet, it is a credit to him and the public service nature of what he has been doing all these years with SG. A difficult post to read:
https://bbs.spamgourmet.com/viewtopic.php?f=5&t=1766&sid=ecd7797eb59f5512879a77eebaa9b40a
@John Warren, thanks for that post about Spamgourmet. I actually registered with this site to comment on the Article, but your post explained to me, in part, what is happening at Spamgourmet. You see I lost my Password wallet in an HDD crash (no backup), and now I not only can’t log in, but seem unable to receive any password reset email.
At least I know what the main problem is. I suspect in blocking some things the guy has inadvertently blocked to password reset email.
I’ve received several of those, probably about 8, there’s probably heaps more, but as I run my own email server on a Linux Box, I have full control over the filters.
At no time did any of the passwords supplied in the email look remotely like any password I have ever used, not that that was much of a clue.
First of all I use a Linux based laptop, so a virus is highly unlikely, not impossible, granted, but not he first, or even the second or third, thing I’d consider.
second I have tape over the built in camera, and a dummy jack in the Microphone socket… paranoia much… but it wouldn’t matter if was doing something salacious in front of my computer.
third all my emails arrive and are display as simple text, not html… which does cause the odd problem reading those emails that insist on html only, but them I check out by viewing the full source first, if it looks suspicious it gets added to my filters, and I never receive one like it again. Fortunately i only need do that at irregular intervals.
And then of course I use lots of Open Source security goodness, and really strong passwords everywhere, to ensure my privacy and security are maintained.
Still ongoing in January 2023, where they only want a mere ‘non-negotiable’ amount of 12.5 Bitcoin (~$17k), lol!
I’m sure they’ll do well asking for such a triflingly small amount – though I may wait a few days when, given it’s volatility, 12.5 bc will likely only be ~$15.00. ![]()
Does anyone fall for this? You’d really have to be completely IT illiterate.
I recommend hosting your email with a company that specializes in, well, email hosting, such as Fastmail or Rackspace.
As an example, Rackspace offers email hosting at $2.40/month per address. (They host more than 20 for me.) Among the advantages is a control panel that enables you to configure your own SPAM settings. I’ve had only one SPAM problem with them in the past 10 years. That one was eventually resolved by Cisco’s SpamCop.
Here is the Apple Mail method that works for me. Select the message and choose
View > Message > Raw Source (Opt-CMD-U)
Edit > Select All
Edit > Copy
Paste this into the Report page at SpamCop. Add a note about any particular suspicion you have. (To file a report, you need to open a free account.)
SpamCOP handles the reporting to the offender’s host for you. It even lobbies on your behalf to sites such as Comcast/Xfinity, the worst offender, in my experience. Reporting SPAM to Comcast daily, using your own Comcast account, has no effect. They just don’t care.